How Systems Protect User Assets
Protecting user assets requires a layered, governance-driven approach. Systems first map valuable assets and likely threats, then implement controls…

Protecting user assets requires a layered, governance-driven approach. Systems first map valuable assets and likely threats, then implement controls…

Sudden price drops arise when incoming trades meet shallow liquidity, triggering rapid price moves as depth is exhausted. Order…
Spam filtering technologies blend rules and machine learning to separate unwanted email from legitimate messages. Core approaches mix crafted…
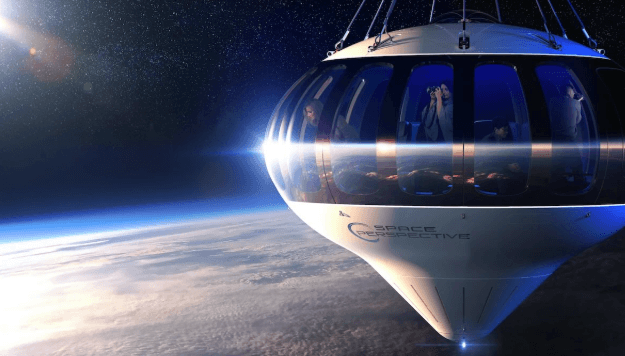
Space tourism today blends brief suborbital access with short orbital missions, inviting non-professionals to the edge of space. It…

Space tech startups are reshaping access to space through modular, cost-conscious architectures across launch, propulsion, and data services. Reusable…
End of content
End of content